Understanding and Resolving the "StartService Failed with Error 4294967201" Error
Introduction
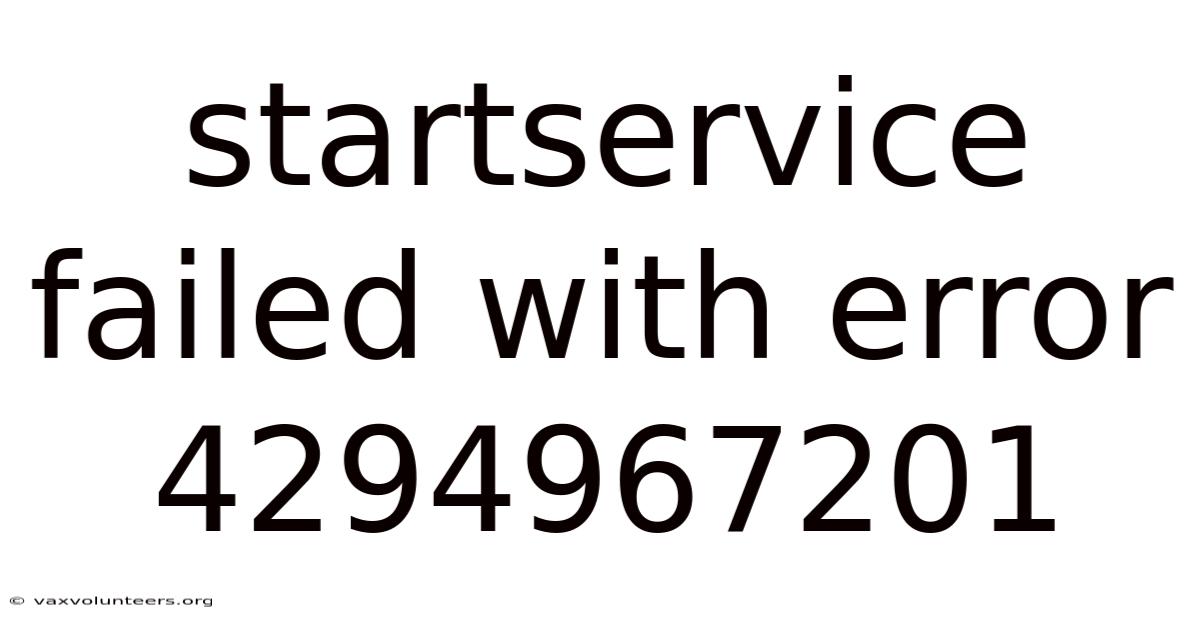
Encountering a "StartService failed with error 4294967201" message on a Windows system can be frustrating, especially when critical services fail to initialize. This error, often logged in the Windows Event Viewer, is tied to the Service Control Manager (SCM)—the core component responsible for managing services in Windows. The error code 0xC0000409 (hexadecimal representation of 4294967201) indicates a generic service startup failure, but diagnosing the root cause requires a systematic approach. This article provides a detailed breakdown of the error, its causes, and actionable solutions to restore service functionality Nothing fancy..
Understanding the Error Code: 0xC0000409
The error 4294967201 (0xC0000409) is a Windows-specific error code generated when the SCM fails to start a service. Unlike more descriptive error messages, this code is intentionally generic, signaling that the SCM encountered an unspecified issue during service initialization. To troubleshoot effectively, users must cross-reference this error with system logs, service dependencies, and configuration settings.
Key Components Involved
- Service Control Manager (SCM):
The SCM acts as the "traffic controller" for services, ensuring they start, stop, and operate correctly. When a service fails to start, the SCM logs the error and halts further execution. - Event Viewer:
The Windows Logs > Application or System logs often contain additional details about the failing service, including its name, process ID, and dependent services.
Common Causes of Error 4294967201
1. Permissions Issues
- Problem: The service may require elevated privileges to run. If the service is configured to run under a user account without administrative rights, the SCM blocks its execution.
- Example: A custom-developed service installed without granting the "Log on as a service" permission to its associated user account.
2. Missing or Corrupted Dependencies
- Problem: Many services rely on other services, drivers, or system components to function. If a dependency is missing, disabled, or corrupted, the SCM cannot start the service.
- Example: A database service failing to start because the SQL Server service is offline.
3. Corrupted Service Files
- Problem: If the service’s executable file (
*.exe) is damaged or incomplete, the SCM cannot load it. This often occurs after abrupt system shutdowns or malware infections.
4. Conflicting Software
- Problem: Third-party applications
5. Conflicting Software or Drivers
When third‑party tools install kernel‑mode drivers, filter drivers, or security agents that hook into the Service Control Manager, they can unintentionally block or race with legitimate services. Antivirus products, system‑optimizers, and even certain Windows updates have been known to interfere with service initialization, especially when they enforce stricter execution policies or modify the service registry entries without proper coordination Turns out it matters..
6. Corrupt Registry Entries
The SCM stores service configuration in the registry under HKLM\SYSTEM\CurrentControlSet\Services. If an entry is malformed—such as an incorrect ImagePath, missing ObjectName, or a corrupted DependOnService list—the manager will reject the service outright. Registry corruption can arise from manual edits, improper uninstallations, or disk‑level errors Nothing fancy..
7. Insufficient Disk Space or I/O Failures
Services often need to write temporary files or configuration data during startup. When the system volume is nearly full or the storage subsystem experiences latency (e.g., a failing hard drive), the SCM may abort the launch process and surface the generic 0xC0000409 error No workaround needed..
Systematic Troubleshooting Workflow
| Step | Action | Expected Outcome |
|---|---|---|
| **1. | Eliminates known bugs that may manifest as generic startup failures. On the flip side, | |
| 6. Use Process Monitor (ProcMon) | Filter the capture to the service’s executable name and watch for ACCESS DENIED, NAME NOT FOUND, or INVALID PARAMETER events during the startup attempt. Correlate these I/O actions with the error timestamps from Event Viewer. Day to day, msc** or sc start <ServiceName>. Test Startup in Safe Mode** |
Reboot into Safe Mode with Networking and attempt to start the service via **Services.That said, export the key for backup before making changes. , certutil -hashfile <path> SHA256). Verify that values such as ImagePath, ObjectName, and DependOnService are syntactically correct and point to existing resources. And microsoft frequently releases patches that address SCM‑related edge cases. g.g.On top of that, g. Worth adding: |
**10. Now, , Start, BinPath, AccountName). In real terms, note the Event ID, Source, and any error sub‑codes that accompany 0xC0000409. |
||
| 5. Practically speaking, review Resource Limits | Check the system’s free disk space (vfs in Task Manager) and verify that the service’s configured Startup type does not exceed the allowed number of concurrent services (rare, but relevant on heavily loaded servers). If it starts successfully, a third‑party filter driver or security software is likely the culprit. Practically speaking, |
Eliminates the “missing dependency” cause and highlights any services that need to be started manually first. Which means |
| **2. | ||
| 3. Re‑register the Service | If the service provides a self‑registration utility (e.Which means | Prevents startup aborts caused by resource exhaustion. Examine Registry Entries** |
| **7. | ||
| 9. Verify Service Dependencies | Use sc queryex <ServiceName> or the Services MMC snap‑in to list the service’s DependOnService chain. |
|
| 4. Compare the hash with a known good version from the vendor or with a clean system backup. Capture Detailed Event Data | Open Event Viewer → Windows Logs → System and locate the most recent entry that references the failing service name. Validate Binary Integrity** | Locate the service executable (BinPath) and compute its hash (e. |
| **8. | Refreshes the SCM’s view of the service configuration without manual registry edits. |
Advanced Diagnostic Techniques
- **Kernel‑Mode Dump Analysis
Advanced Diagnostic Techniques (continued)
-
Kernel‑Mode Dump Analysis
- When a service fails to start, the fault may originate in a kernel‑mode driver that the service loads (e.g., a filter driver, file‑system mini‑filter, or NDIS protocol). Capture a kernel memory dump (Complete or Kernel) at the moment of failure by configuring the system for automatic crash dumps (
SystemProperties → Advanced → Startup and Recovery → Write debugging information). - Load the dump in WinDbg (
!analyze -v) and look for the thread that calledNtCreateUserProcessorNtLoadDriver. The stack trace will often reveal the offending driver name and the exact NTSTATUS code (e.g.,0xC0000022for access denied,0xC00000BBfor invalid image hash). - If the dump shows a BUGCODE_ID_DRIVER or PAGE_FAULT_IN_NONPAGED_AREA, update or roll back the implicated driver, or temporarily disable it via
sc config <driver> start= disabledto verify whether the service starts.
- When a service fails to start, the fault may originate in a kernel‑mode driver that the service loads (e.g., a filter driver, file‑system mini‑filter, or NDIS protocol). Capture a kernel memory dump (Complete or Kernel) at the moment of failure by configuring the system for automatic crash dumps (
-
Event Tracing for Windows (ETW) – Service Control Manager Provider
- Enable the Microsoft‑Windows‑ServiceControlManager‑Operational channel (
wevtutil sl Microsoft-Windows-ServiceControlManager/Operational /e:true) and set its level to Verbose. - Reproduce the failure, then save the log (
wevtutil epl Microsoft-Windows-ServiceControlManager/Operational SCM.etl). - View the trace in Windows Performance Analyzer (WPA) or Message Analyzer; look for events such as
ServiceStartFailed,ServiceStartTimeout, orServiceStartAttempt. The associatedErrorCodefield maps directly to Win32/NTSTATUS values, giving a precise failure reason without needing to guess from generic Event Viewer entries.
- Enable the Microsoft‑Windows‑ServiceControlManager‑Operational channel (
-
Process Explorer – Handle and DLL Views
- Start Process Explorer with elevated privileges, locate the service’s
svchost.exe(or the service‑specific executable) in the process tree, and examine:- Handles: Filter for
KEY,FILE, orDEVICEobjects that returnACCESS DENIED. A missing registry key or a file locked by another process often surfaces here. - DLLs: Verify that all dependent DLLs are loaded from the expected paths. A DLL hijack (e.g., a malicious copy placed earlier in the PATH) will cause the service to initialize incorrectly and abort during
DllMain.
- Handles: Filter for
- Start Process Explorer with elevated privileges, locate the service’s
-
Dependency Chain Validation with
sc queryexandsc dependent- Services often fail because a required dependency is stopped, disabled, or itself failing. Run:
sc queryexsc dependent - For each dependency, repeat the validation steps (binary integrity, registry, permissions). If a dependency is marked
START_TYPE = DISABLED, change it toAUTOorDEMAND_STARTand test again.
- Services often fail because a required dependency is stopped, disabled, or itself failing. Run:
-
Security Auditing – SACL on Service Objects
- If the service runs under a dedicated service account, confirm that the account has the “Log on as a service” right (
secpol.msc → Local Policies → User Rights Assignment). - Additionally, inspect the System Access Control List (SACL) on the service’s registry key (
HKLM\SYSTEM\CurrentControlSet\Services\<ServiceName>) for audit entries that might be generatingACCESS DENIEDevents in the Security log. Enabling auditing (auditpol /set /subcategory:"Kernel Object" /success:enable /failure:enable) can reveal whether the SCM is being blocked by a policy rather than a missing permission.
- If the service runs under a dedicated service account, confirm that the account has the “Log on as a service” right (
-
Repairing the Service Control Manager Database
- Persistent startup failures can sometimes be traced to a corrupted Services database (
%SystemRoot%\System32\config\SYSTEM). - Boot into the Windows Recovery Environment, launch Command Prompt, and run:
reg delete HKLM\TEMP_SYSTEM\CurrentControlSet\Services\/f reg unload HKLM\TEMP_SYSTEM - After removing the problematic key, reboot normally and reinstall the service (via its installer or
sc create). This forces the SCM to rebuild the entry from scratch.
- Persistent startup failures can sometimes be traced to a corrupted Services database (
-
**Using the Windows Debugger (WinDbg) – User‑
7. Using the Windows Debugger (WinDbg) – User‑mode debugging of the service process
- Attach to the failing instance – If the service crashes shortly after start, configure it to launch under a debugger:
The service will be spawned under WinDbg, breaking immediately on entry.sc configtype= own start= demand sc failure reset= 0 actions= run/"C:\Debuggers\windbg.exe" -g -G -p %1 sc start - Set a breakpoint on the service’s entry point – Most services expose a
ServiceMainfunction; you can locate it withx <module>!ServiceMainand thenbp <module>!ServiceMain. - Examine the call stack on the first‑chance exception – When the service throws, WinDbg will break. Use
kto view the stack; look for frames inside your own DLLs or third‑party components. A recurring pattern such asntdll!RtlUserThreadStart → <your dll>!Init → …often points to initialization code that fails due to a missing resource or a corrupted global. - Inspect registers and memory – If the exception is an access violation (
0xC0000005), note the faulting address (eax/ripon x64). Usedd <address>ordp <address>to see whether the pointer references a module that failed to load, a freed heap block, or an unmapped region. - Check loader events – Enable loader snaps with
sxe ld:<module>to break whenever a DLL is loaded. This helps catch DLL‑hijack scenarios where an unexpected copy is pulled from a directory earlier in the PATH. - Log output – Use
.logopen c:\temp\service_dbg.logbefore reproducing the failure, then.logcloseafter the crash. The log captures all debugger commands and output, making post‑mortem analysis easier when you cannot reproduce the issue interactively.
8. Capturing and Analyzing a Crash Dump
- Configure the service to generate a full user‑mode dump on second‑chance exceptions: ```cmd
reg add "HKLM\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps<ServiceName>" ^
/v DumpType /t REG_DWORD /d 2 /f &&
reg add "HKLM\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps<ServiceName>" ^
/v DumpFolder /t REG_EXPAND_SZ /d "C:\CrashDumps" /f && reg add "HKLM\SOFTWARE\Microsoft\Windows\Windows Error Reporting\LocalDumps<ServiceName>" ^
/v DumpCount /t REG_DWORD /d 10 /f
- After the service fails, locate the newest
.dmpfile in the specified folder. Open it in WinDbg with!analyze -v. The analyzer will summarize the exception, list loaded modules, and often point directly to the offending function or DLL. - If the dump shows a stack overflow (
0xC00000FD), increase the service’s stack size via theStackSizevalue under its registry key or redesign the recursive algorithm.
9. Process Monitor (ProcMon) – Fine‑grained file/registry activity
- Start ProcMon with a filter:
Process Name is <service exe>andOperation is RegOpenKey or RegCreateKey or CreateFile or ReadFile. - Reproduce the failure and look for
RESULT: NAME NOT FOUND,RESULT: ACCESS DENIED, orRESULT: PATH NOT FOUND. These entries often reveal a missing configuration file, a misplaced DLL, or a registry value that the service expects but
10. Interpreting ProcMon Results – From Noise to Actionable Insight
When the filter above surfaces a RESULT: NAME NOT FOUND entry, the first instinct is to locate the missing key or file. That said, the real power of ProcMon lies in correlating that event with the service’s internal state:
-
Map the Path to a Configuration Source – If the missing path points to a registry value (e.g.,
HKLM\Software\MyService\Parameters\Endpoint), open the registry editor and verify that the value exists and contains the expected data type. A common pitfall is a DWORD stored as a string, which can cause the service to treat the address as invalid and crash during parsing Simple as that.. -
Trace the File’s Ancestor Directory – ProcMon records the full path of every file operation. By right‑clicking the entry and selecting “Open File Location,” you can inspect the directory hierarchy. Often the service expects a configuration file in a sub‑folder that is created only after an earlier initialization step. If that step failed silently, the directory never materializes, leading to the later “file not found” error.
-
Check for Unexpected Redirection – Windows services sometimes rely on environment variables (e.g.,
%ProgramData%,%LOCALAPPDATA%). If a redirection tool such as AppCompat or a corporate policy modifies these variables after the service has started, ProcMon will show aPATH NOT FOUNDfor a file that was previously accessible. Capture the environment at startup withset > C:\Temp\env.txtand compare it to the runtime environment logged by ProcMon. -
Correlate with Timing – Use the “Time of Day (ms)” column to align the failing operation with other events captured by Debugging Tools for Windows (e.g., a loader snap that unloads a DLL just before the file access). This temporal correlation can expose race conditions where a dependent component is torn down prematurely.
-
Automate Repetition – For services that exhibit intermittent failures, script a loop that repeatedly triggers the problematic scenario while ProcMon records. Export the log to CSV and employ a simple PowerShell filter to isolate entries with
RESULT: ACCESS DENIED. This approach surfaces patterns that are invisible in a single manual run.
11. Advanced Debugging Techniques
-
Heap and Memory Corruption Checks – When the service crashes with an access violation inside a third‑party library, enable heap validation by adding
gflags /i <service.exe> +hpabefore launching the service. The resulting dump will contain!heap -soutput that highlights overrun or double‑free conditions. Combine this with!analyze -vto see if the faulting instruction resides in a known vulnerable module. -
Thread‑Pool Exhaustion Detection – Services that rely heavily on asynchronous I/O may hit the default thread‑pool limit (512 threads). Use
!pool -allocator Lookasideto inspect pool usage, and monitor theThreadPoolperformance counters (ThreadPool\Thread Count). If the pool saturates, consider raising theMaximumThreadsregistry value or redesigning the concurrency model. -
Power‑Management Interference – On systems configured for aggressive power‑saving, a service may be throttled or suspended just before it accesses a critical resource. Enable
PowerCfg -requeststo view active power requests, and disable theAllow the computer to turn off this device to save poweroption for the relevant hardware interfaces Simple as that.. -
Network‑Stack Diagnostics – If the service communicates over TCP/UDP, capture the socket state with
netstat -anoand cross‑reference the PID. Use!sym noisyin WinDbg to force symbol loading for the networking stack, which can reveal missing Winsock DLLs or corruptedWS2_32.dllentries.
12. When All Else Fails – Structured Post‑Mortem Reporting
A systematic post‑mortem not only documents the failure but also creates a reusable knowledge base:
-
Create a Failure Artifact Package – Bundle the crash dump, ProcMon CSV, Debugging Tools log, and a screenshot of the service’s Event Viewer entries into a timestamped ZIP file. Include a short README that lists the exact command line used to reproduce the issue Nothing fancy..
-
Populate a Root‑Cause Matrix – For each symptom (e.g., “Access violation in
kernel32!VirtualAllocEx”), record:- Time of occurrence
- Loaded modules at that moment
- Register values that led to the fault
- Immediate preceding ProcMon event
- Hypothesized cause (missing file, race condition, resource limit)
-
Assign Ownership and Next Steps – Tag each matrix entry with a responsible engineer, a target resolution date, and any required code changes or configuration updates. This ensures that the investigation does not dissolve into an undocumented pile of logs That alone is useful..
-
Archive the Learnings – Store the matrix and artifact package in a version‑controlled repository (e.g., Git) under a
under a dedicated directory named afterthe service and incident identifier (e.Within this folder, place the ZIP artifact package alongside a README.g.That's why , services/MyService/incidents/2024-09-26_001). md that captures the exact reproduction steps, the debugger command line used, and any environment variables that were altered for the test It's one of those things that adds up..
You'll probably want to bookmark this section Worth keeping that in mind..
Link each incident folder to an entry in your issue‑tracking system (Jira, Azure DevOps, GitHub Issues, etc.) by adding a comment that contains the relative path to the repository. This creates a bidirectional traceability: engineers can jump from a ticket straight to the raw evidence, and auditors can verify that every reported symptom has a corresponding artifact set.
To turn the raw matrix into actionable insight, export it as a CSV or JSON file and run a lightweight script that aggregates frequency counts per root‑cause category (e.That said, g. When a root cause is confirmed, update the service’s documentation and runbooks to reflect the new mitigation (e.Visualizing these aggregates with a simple bar chart in a markdown file helps teams spot systemic patterns—such as a particular subsystem repeatedly triggering heap overruns—prompting targeted refactoring or configuration changes rather than ad‑hoc fixes. g., increased MaximumThreads value, added power‑request exception, or revised error‑handling around VirtualAllocEx). , “missing DLL”, “thread‑pool exhaustion”, “power‑throttle”). Tag the corresponding commit with the incident ID so future developers can see exactly why a particular guardrail exists Not complicated — just consistent..
Finally, schedule a brief retrospective meeting after each major incident. Use the artifact package as the focal point: walk through the timeline, validate the hypothesized cause against the recorded register state and ProcMon events, and agree on any follow‑up actions (unit tests, stress‑test scenarios, or monitoring alerts). Capture the meeting minutes in the same repository folder, ensuring that the knowledge gained from the failure is preserved alongside the technical evidence.
By consistently applying this structured post‑mortem workflow, teams transform isolated crashes into a living repository of failure patterns, preventive measures, and institutional memory—turning debugging from a reactive fire‑fight into a proactive engineering discipline Less friction, more output..
Conclusion Effective service troubleshooting on Windows hinges on a layered strategy: start with lightweight, real‑time monitors (ProcMon, performance counters, power‑cfg requests), progress to deep‑dive debugging techniques (heap validation, thread‑pool inspection, symbol‑rich WinDbg analysis), and, when needed, employ network‑stack diagnostics to isolate external dependencies. If the issue persists, a disciplined post‑mortem—complete with artifact packaging, root‑cause matricing, ownership tracking, and version‑controlled archiving—ensures that every lesson learned is captured, shared, and turned into concrete improvements. Following this systematic approach not only resolves the immediate fault but also builds a resilient foundation that reduces the likelihood of similar failures in the future.