Introduction
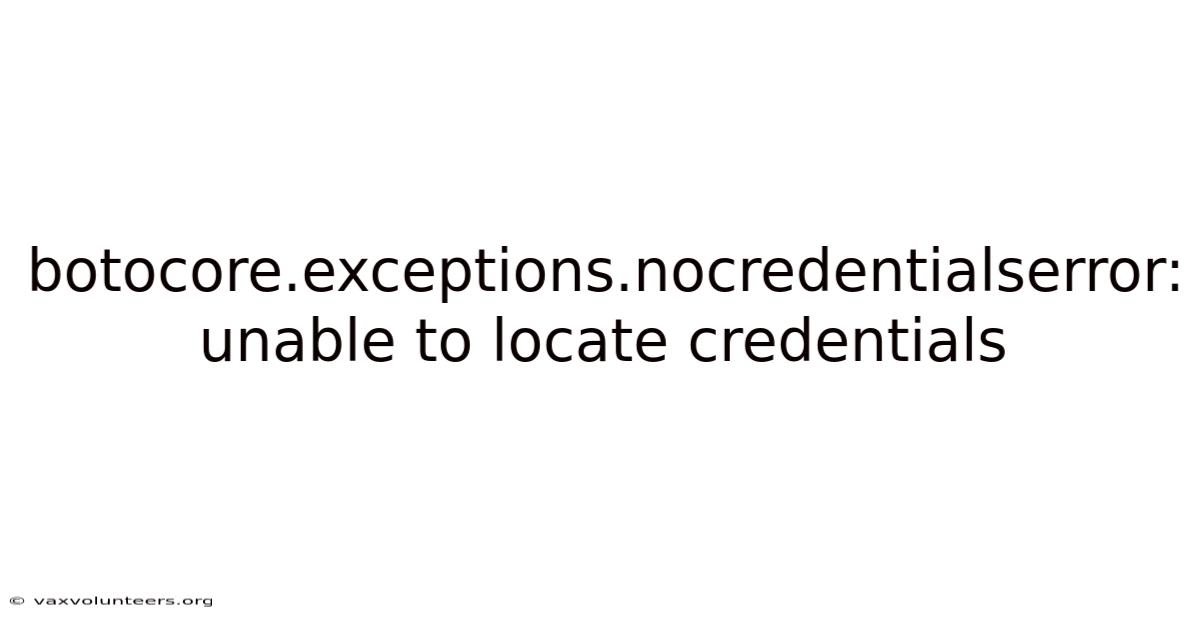
The botocore.nocredentialserror: unable to locate credentials error is a common issue encountered by developers working with AWS (Amazon Web Services) SDKs and tools. This error occurs when the AWS SDK cannot find valid credentials to authenticate and authorize requests to AWS services. exceptions.Understanding this error and how to resolve it is crucial for anyone working with AWS programmatically, as it forms the foundation of secure and functional cloud operations.
Detailed Explanation
The botocore.On the flip side, nocredentialserror is part of the Botocore library, which serves as the foundation for the AWS SDK for Python (Boto3). exceptions.Consider this: botocore handles the low-level communication between your Python application and AWS services. When you attempt to make an AWS API call without providing valid credentials, Botocore raises this exception to prevent unauthorized access attempts.
Credentials in AWS can be provided through multiple methods: environment variables, AWS credentials profile file, IAM roles (for EC2 instances), or explicit credential parameters in your code. In real terms, the SDK searches for credentials in a specific order of precedence, and if none are found or if the found credentials are invalid, the NoCredentialsError is triggered. This error acts as a security mechanism to make sure only properly authenticated requests reach AWS services Worth keeping that in mind..
This changes depending on context. Keep that in mind.
Step-by-Step Credential Resolution Process
When your application attempts to connect to AWS, Botocore follows a specific credential resolution chain. Next, it searches the AWS credentials file located at ~/.aws/credentials on Unix-based systems or C:\Users\USERNAME\.Which means first, it checks for credentials passed directly as parameters in your code. If none are found, it looks for environment variables like AWS_ACCESS_KEY_IDandAWS_SECRET_ACCESS_KEY. aws\credentials on Windows.
And yeah — that's actually more nuanced than it sounds.
If credentials still aren't found, Botocore checks for IAM roles if your code is running on an EC2 instance, ECS container, or Lambda function. aws/config. On top of that, finally, it looks for credentials configured in the AWS config file at ~/. Understanding this chain helps in troubleshooting where the credential lookup is failing and why the error occurs.
Real Examples
Consider a scenario where you're developing a Python script to upload files to S3. Your code might look like this:
import boto3
s3 = boto3.client('s3')
s3.upload_file('local_file.txt', 'my-bucket', 'remote_file.txt')
If you run this code without any credentials configured, you'll immediately encounter the NoCredentialsError. This happens because the SDK has no way to authenticate your request to S3. Another common scenario occurs when developers set up credentials in one terminal session but run their code in a different terminal or IDE, where the environment variables aren't available The details matter here. Practical, not theoretical..
In production environments, this error often appears when deploying applications to servers or containers without properly configuring IAM roles or when using CI/CD pipelines that don't have the necessary AWS credentials injected into the build environment.
Scientific or Theoretical Perspective
From a security architecture perspective, the NoCredentialsError represents a fundamental principle of the principle of least privilege and secure default configurations. By requiring explicit credential provision, AWS ensures that applications cannot accidentally make unauthorized requests. This aligns with the broader security concept of "fail closed" - when a system encounters uncertainty about authorization, it defaults to denying access rather than potentially allowing unauthorized operations.
The credential resolution mechanism also demonstrates the concept of layered security through multiple authentication methods. Each credential source represents a different trust boundary: direct code parameters (highest trust but least convenient), environment variables (moderate trust), credential files (persistent but file-system bound), and IAM roles (dynamic, instance-bound credentials). This multi-layered approach provides flexibility while maintaining security Took long enough..
Common Mistakes or Misunderstandings
One frequent misunderstanding is assuming that installing Boto3 automatically provides AWS credentials. Developers often install the SDK and immediately try to run code, only to be surprised by the credential error. Another common mistake is confusing IAM users with IAM roles - while both provide credentials, they serve different purposes and have different configuration methods.
Developers sometimes also overlook the importance of credential file syntax. Now, the AWS credentials file requires a specific format with profile names and key-value pairs. A simple typo or incorrect formatting can cause the SDK to fail credential discovery. Additionally, many developers forget that credentials expire, especially when using temporary credentials from IAM roles or federation, leading to intermittent credential errors that can be challenging to debug No workaround needed..
You'll probably want to bookmark this section It's one of those things that adds up..
FAQs
Q: How do I fix the NoCredentialsError in my local development environment?
A: The most straightforward solution is to configure the AWS CLI on your machine, which creates the necessary credentials file. Run aws configure in your terminal, provide your access key and secret key when prompted, and the SDK will automatically find these credentials. Alternatively, you can set the AWS_ACCESS_KEY_ID and AWS_SECRET_ACCESS_KEY environment variables.
Counterintuitive, but true.
Q: Why does my code work on my local machine but fails in production?
A: This typically happens when your local machine has configured credentials but your production environment doesn't. In production, you should use IAM roles rather than static credentials. For EC2 instances, attach an appropriate IAM role. For containers or Lambda functions, configure execution roles with the necessary permissions Simple, but easy to overlook..
This changes depending on context. Keep that in mind.
Q: Can I bypass this error by hardcoding credentials in my code?
A: While technically possible, hardcoding credentials is strongly discouraged as it creates significant security risks. If your code is in version control or shared, your credentials could be compromised. In real terms, additionally, hardcoded credentials make rotation and management difficult. Always use secure credential storage methods like IAM roles or external credential management systems.
Q: How can I programmatically check if credentials are available before making API calls?
A: You can use the boto3.Consider this: get_credentials() method to check for available credentials. If this returns None, you know credentials aren't configured. Session().You can also catch the NoCredentialsError exception specifically to handle credential-related failures gracefully in your application.
Conclusion
The botocore.So understanding the credential resolution process, common configuration methods, and best practices for credential management is essential for any developer working with AWS services. That said, exceptions. nocredentialserror: unable to locate credentials error, while initially frustrating, serves as an important security safeguard in AWS SDK operations. And by properly configuring credentials through secure methods like IAM roles or credential files, and understanding the credential resolution chain, you can ensure your applications connect to AWS services reliably and securely. Remember that this error isn't just a technical hurdle but a fundamental aspect of AWS's security model, designed to protect both your resources and the broader AWS ecosystem.
When troubleshooting the NoCredentialsError, it's helpful to understand the order in which boto3 searches for credentials. In practice, the SDK follows a specific chain: first checking environment variables, then shared credential files, then IAM roles (if running on an EC2 instance or similar), and finally configuration files. This hierarchy means that credentials configured at one level can override those at another, which is useful but can also lead to confusion if you're not aware of all the sources It's one of those things that adds up. That alone is useful..
If you're working in a containerized environment or deploying to a serverless platform like AWS Lambda, the approach to credential management shifts. In these cases, relying on IAM roles assigned to the execution environment is the most secure and scalable option. This eliminates the need to manage static credentials altogether and aligns with the principle of least privilege by granting only the permissions necessary for the application to function Surprisingly effective..
For local development, using the AWS CLI to configure credentials is often the quickest path to resolution. In practice, the aws configure command creates a profile in the ~/. Also, aws/credentials file, which boto3 will automatically detect. If you need to switch between multiple AWS accounts or roles, you can create and manage multiple profiles, specifying which to use in your application code when creating a session.
It's also worth noting that credential-related errors can sometimes be masked by other issues, such as network misconfigurations or IAM policy restrictions. If you've confirmed that credentials are properly configured but still encounter errors, verify that the credentials have the necessary permissions for the intended operation and that your network allows connections to AWS endpoints.
Conclusion
The botocore.So exceptions. Worth adding: nocredentialserror: unable to locate credentials error is a common but solvable issue that underscores the importance of secure credential management in AWS environments. That said, by understanding the credential resolution process, leveraging IAM roles for production workloads, and using secure local configurations for development, you can avoid this error and maintain a reliable security posture. Which means always prioritize secure practices over quick fixes, and remember that proper credential management is not just about resolving errors—it's a critical component of protecting your AWS resources and data. With the right approach, you can ensure your applications connect to AWS services naturally and securely, both in development and in production Small thing, real impact. That alone is useful..